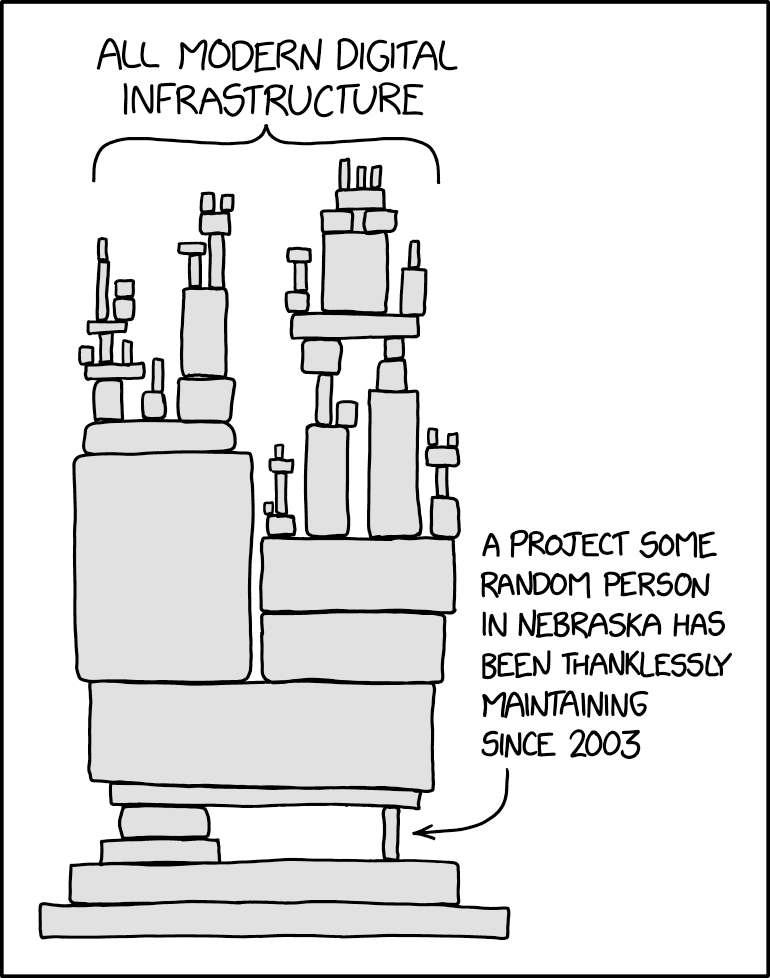
This is why you do staged rollouts of updates... not the entire planet at once.
Technology
This is a most excellent place for technology news and articles.
Our Rules
- Follow the lemmy.world rules.
- Only tech related content.
- Be excellent to each another!
- Mod approved content bots can post up to 10 articles per day.
- Threads asking for personal tech support may be deleted.
- Politics threads may be removed.
- No memes allowed as posts, OK to post as comments.
- Only approved bots from the list below, to ask if your bot can be added please contact us.
- Check for duplicates before posting, duplicates may be removed
Approved Bots
And don't have automatic updates enabled for critical infrastructure.
So true, this really highlights the risk of updates impacting critical systems vs critical systems being exposed to critical vulnerabilities. Its a real balancing act.
I don't know exactly how crowd strike works, but this sounded like a "virus signatures" update (IE not a software update per se). And thats what caused the issue.
I think "real time virus protection" is why people use it so they expect the signatures to get updated asap/with little to no human intervention.
This is a crowd strike epic fail...for how they let their software blue screen systems with a virus signature update.
Can someone in non marketing terms explain what the fuck CrowdStrike Falcon Sensor is? I literally never heard of this company or product before.
It's basically corporate anti-virus software. Intended to detect and prevent malware.
Apparently it's the next iteration of AI based antivirus where it uses smart algorithms to detect system behaviours and makes assessments on whether they're malicious or not
Apparently it's the next iteration of AI based antivirus
CrowdskyStrikenet
I know there is a lot of marketing fluff, but yes, it is an EDR. Which means instead of just checking file signatures against a database if known bad stuff, it actually examines what applications do and makes a sort of judgement on if it is acting maliciously or not. I use a similar product. Although the false positives can sometimes be baffling, it honestly can catch a legit program misbehaving.
On top of that, everything is logged. Every file, network connection, or registry key that every process on the computer touches is logged. That means when something happens, you can see the full and complete list of actions taken by the malicious system. Thus can actually be a drain on the computer, but modern systems handle it well enough.
obviously, A.I consider microsoft as a malicious software. Sometimes, A.I is very accurate 😁
It checks for malicious falcons in your system's level 4 aviary cache.

It's software put on every machine so that the company can quickly isolate it if/when something bad happens (or it falls out of security compliance). To do this is requires a constant Internet connection, insanely high privileges on the machine and frequent updates to be appraised of risks.
That risk update went off the rails and into the next state.
I work in QA on the night shift at a video game company. It was absolute chaos at work tonight lmao we only had a grand total of 6 working PCs between all of us
Company spyware. We have that on our devices. They used to have an “about” stored locally on the app, but removed it and a web connection is required to view the docs. Basically says it downloads/sees everything on your device and checks for threats. Thing is a few people have been fired for having things in their devices they shouldn’t. I didn’t ask what it was, nor did I hear how these things were “threats”, but nonetheless they were fired. Too many people treat company hardware like “free device, bro!” and put all sorts of personal stuff on the device. Most industries it’s probably not too big of a deal, but for mine if there’s an incident that happens when you were busy watching Netflix or something instead of doing your job you’re fucked. First thing they’ll do is check your device and crowdstrike to see what you were doing, and even if you weren't watching Netflix all your personal data will be exposed.
They definitely could, but most cybersecurity departments are paid too much to worry about minor items like that. If HR tells us to look into a specific user and gets the proper approvals so that everything is in compliance, we'll definitely get someone on the team to do it, but otherwise if we happen to see evidence of unapproved usage, we're mostly going to overlook it unless it could lead to something dangerous to your machine or the company as a whole.
EDRs like Crowdstrike can see very very nearly everything you do though, definitely everything you would care about.
Yikes. I feel sorry for all the help desk and support staff that has to deal with this chaotic mess all day.
On a Friday !
What kind of criminally incompetent psychopath rolls out a global update on a fucking Friday afternoon?
Is the CEO of CrowdStrike Satan?
They push updates every day. Attackers don't take Fridays off.
Yup, my phone is nonstop going off with slack messages and tickets. Time to mute it for now
What a striking name... CrowdStrike heh. They definitely live up to it!
More like CrashStrike
This is going to turn out it was a hack in several months right?
Won't take that long, security researchers are already decompiling the update to see if it was malicious or incompetence.
This is going to be Solarwinds all over again I can just smell it.
Hacks of this grade tend to be targeted, this is most likely incompetence.
A lot of companies will get calls from the "provider" offering help with mitigation so that additional features can also be installed. This is a time to be extra wary.
Edited: spelling
Never attribute to maliciousness that which can be explained by incompetence.
That said, I'm sure the Crowdstrike CEO is currently on a phone call with three of their pet Congresscritters asking if they can get a $100M grant to harden their systems against Russia/China/NKorea/Antifa interference right now.
"Senator, we were hacked by gay furries."
"We need to get more of our own gay furries! There's a gay furry gap!"
If I ever become a super 1337 hacker I'm going to setup all of my exploits to look like it could be regular mismanagement, thanks for the advice
I'll just quietly leave this here: https://www.crowdstrike.com/blog/crowdstrike-google-cloud-expand-strategic-partnership/
Ca-caw!
Looking forward to the Kevin Fang video in a few years.