SSL Certs were so god awful before certbot that it’s hard to explain now that it’s so easy and free.
Technology
This is a most excellent place for technology news and articles.
Our Rules
- Follow the lemmy.world rules.
- Only tech related content.
- Be excellent to each another!
- Mod approved content bots can post up to 10 articles per day.
- Threads asking for personal tech support may be deleted.
- Politics threads may be removed.
- No memes allowed as posts, OK to post as comments.
- Only approved bots from the list below, to ask if your bot can be added please contact us.
- Check for duplicates before posting, duplicates may be removed
Approved Bots
Lol I instinctively freaked out when I saw the post preview assuming it was going to be a post about a major data breach or exploit of some sort relating to Let's Encrypt.
I probably need more positivity in my life 😂
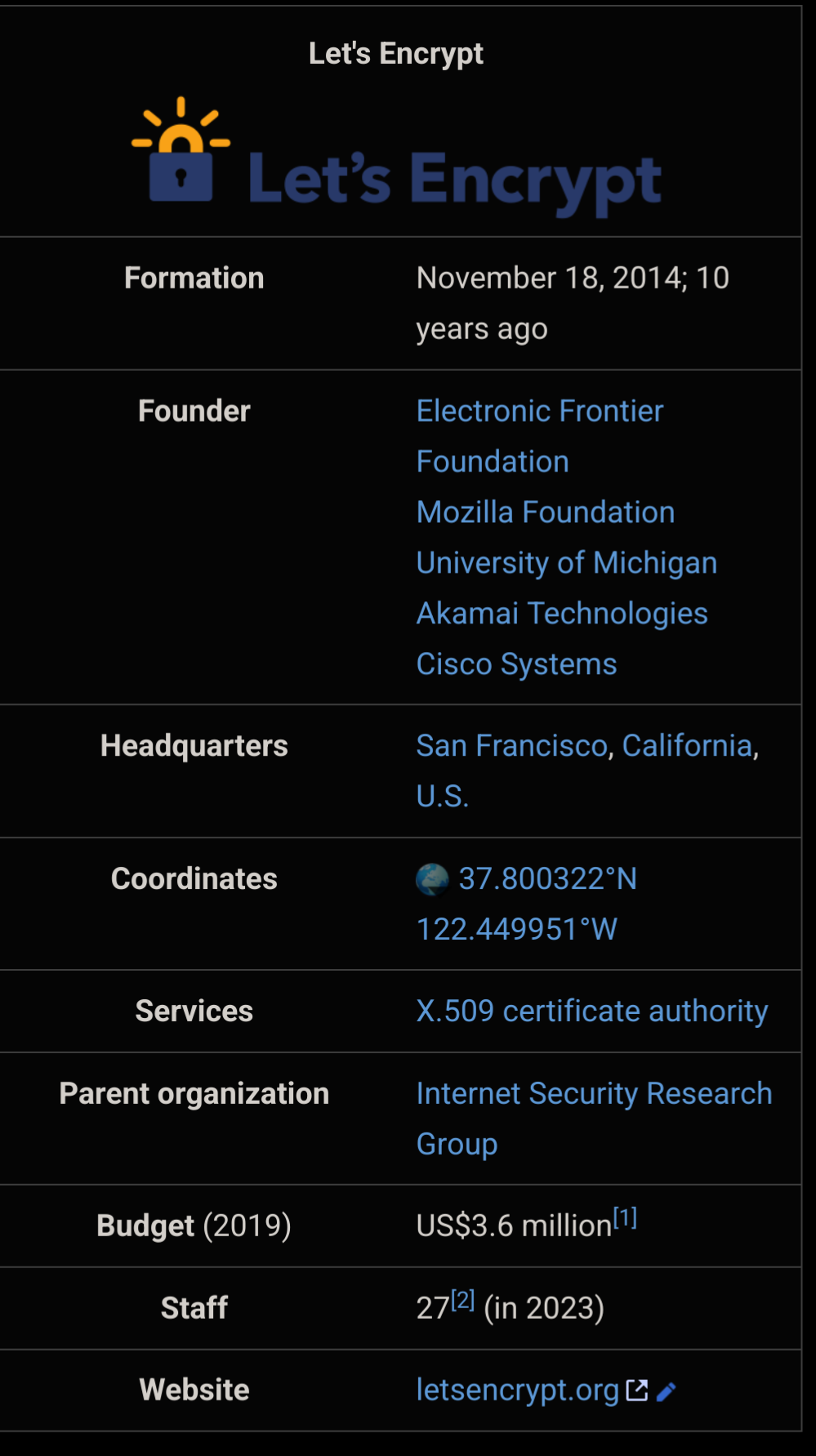
Huge impact on a tiny budget - that’s extremely impressive. The world could be so much better without rent seeking parasites.
Underrated. Stuff rocks.
And it changed the Internet, for good and a lot.
Man I love let's encrypt, remember how terrible ssl was before the project landed?
I always had to fill out multiple pages of forms to get those free 1 year "trial" certs from startssl.
Oh man, I forgot about startssl until just now. I definitely had a few of those certs. If you wanted something fancy like a wildcard cert back then, you were paying $$$
Remember they wanted like $75 for certs? The gall.
Crazy times. Nowadays it's weird when a website doesn't have https. Back then it was pretty much big companies only. And the price of a wildcard certificate...
Except for neverssl.com
Triggering the launch of captive portals for public Wi-Fi users everywhere yayy
And if you remember, that this whole shebang was only started, because Snowden revealed that the NSA spied on all of us, it's getting much much darker.
I did not have the money to pay the insane amounts these greedy for-profit certificate authorities asked, so I only remember the pain of trying to setup my self-signed root certificate on my several devices/browsers, and then being unable to recover my private key because I went over the top with securing it.
Damn! That's definitely a "I'm old" moment for me. I still remember when I first heard about the concept and I remember setting it up the first time on a self hosted project (which seemed harder back then).
Awesome project!
Let's Encrypt is amazing, but are there any equally trustworthy alternatives people could switch to if something bad happens to it?
They came up with the ACME protocol, so presumably somebody could. The real barrier to entry is the cost of getting into that certificate chain of trust. I have no idea why it's so difficult and expensive.
Well, it's difficult, as it should be, because if you control a certificate in the active chain of trust of browsers, you can hack pretty much anything you want.
Correct me if I'm wrong, but isn't the CA only signing your public key to prove identity/authority? I don't think the CA can magically MITM every cert they sign.
The impact is serious enough to warrant a $1m entry fee, IMO. At best, someone could impersonate a site. They'd also have to get other things in line (e.g. DNS hijacking) to be at all successful anyway. And it's not like most people are authenticating certs themselves. They just trust browsers to trust CAs that vouch for you and prevents those scary browser warnings.
It doesn't improve encryption compared to a self-signed cert though.
If you are the CA, you can sign a new certificate yourself for google.com and the browser will accept it. It's effectively allows MITM for any certificate. Worse, it's not even limited to certificates under that CA. The browser has no way of knowing there's 2 "valid" certs at once, and in fact that is allowed regardless (multiple servers with different instances of the SSL cert is a possibility).
Certificate pinning might save things, since that will force the same certificate as was previously used, but I'm not sure this is a common default.
If it begins to enshitify, someone will quickly take up the helm. It's become so core now that someone like Cloudflare would just be like "We do this now."
Cloudflare sort of provides this now by being a MITM to secure your site between your server and the end user. But this requires you and your end user to trust Cloudflare.
And fwiw the ACME protocol is open so anyone can implement it. I believe even the ACME software that EFF sends out allows you to choose your server with some configuration.
Maybe ZeroSSL
Yay for their glorious, free trusted ssl certs. Love this project!