Wireguard.
Unless you actually have a need for the public to access the services then you shouldn't be exposing them. If it's just you and a few household members that need access then you should be using ddns and wireguard, or similar.
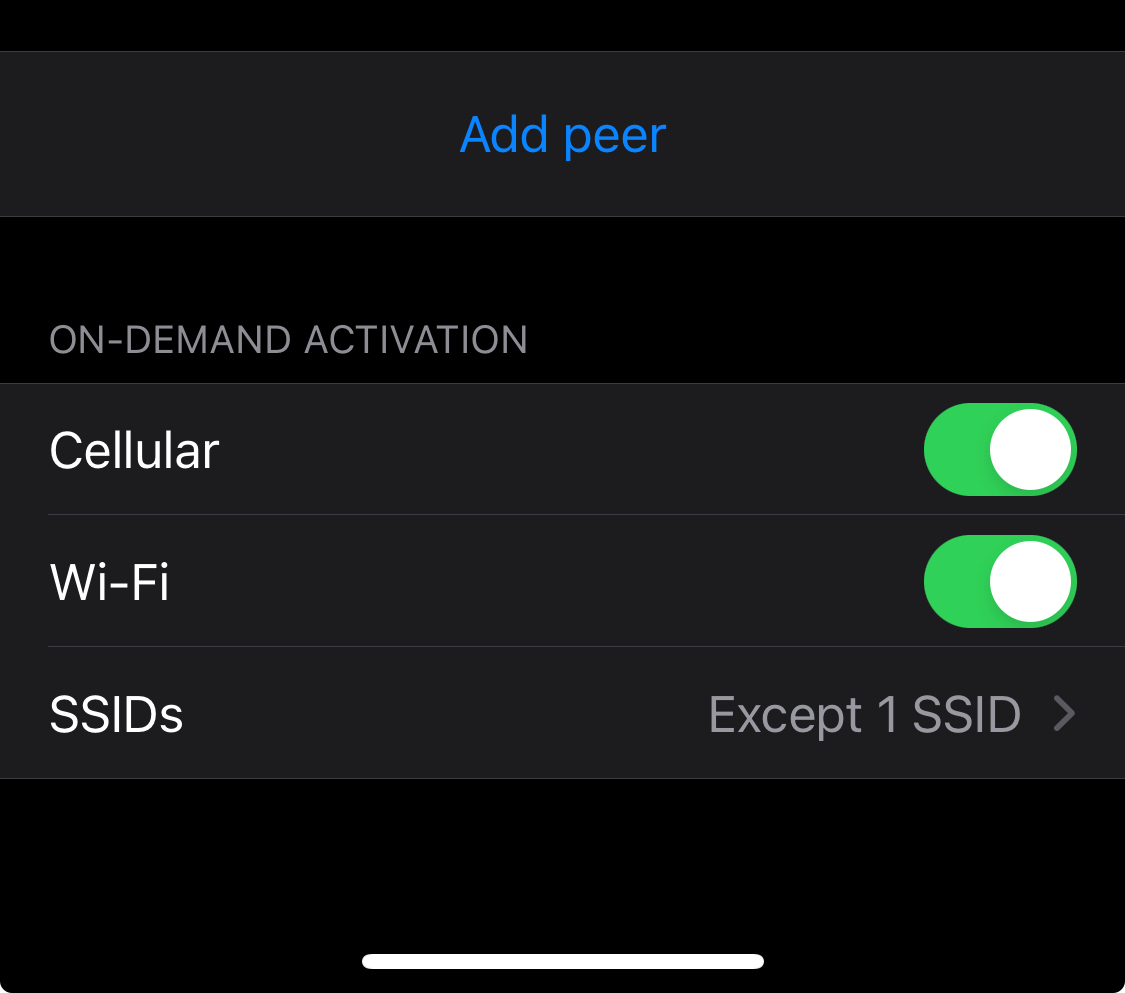
My phone auto connects with wireguard as soon as I leave my home ssid, so I never lose access to my services.