Yeah, don't do this, and you should be fine.
This is the official technology community of Lemmy.ml for all news related to creation and use of technology, and to facilitate civil, meaningful discussion around it.
Ask in DM before posting product reviews or ads. All such posts otherwise are subject to removal.
Rules:
1: All Lemmy rules apply
2: Do not post low effort posts
3: NEVER post naziped*gore stuff
4: Always post article URLs or their archived version URLs as sources, NOT screenshots. Help the blind users.
5: personal rants of Big Tech CEOs like Elon Musk are unwelcome (does not include posts about their companies affecting wide range of people)
6: no advertisement posts unless verified as legitimate and non-exploitative/non-consumerist
7: crypto related posts, unless essential, are disallowed
Yeah, don't do this, and you should be fine.
But I need to know which Harry Potter character I am!!
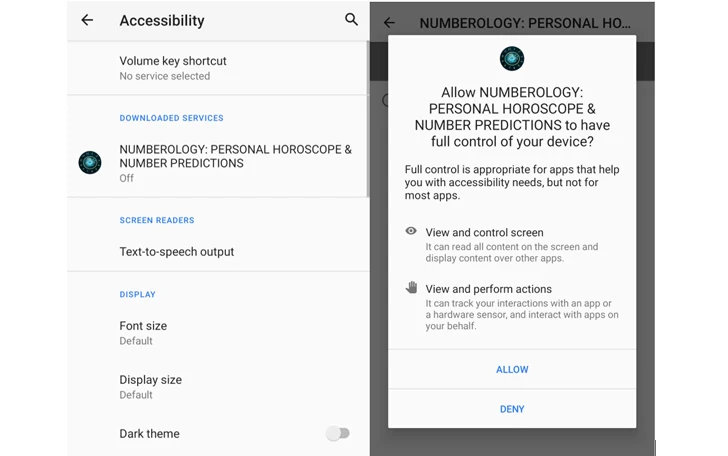
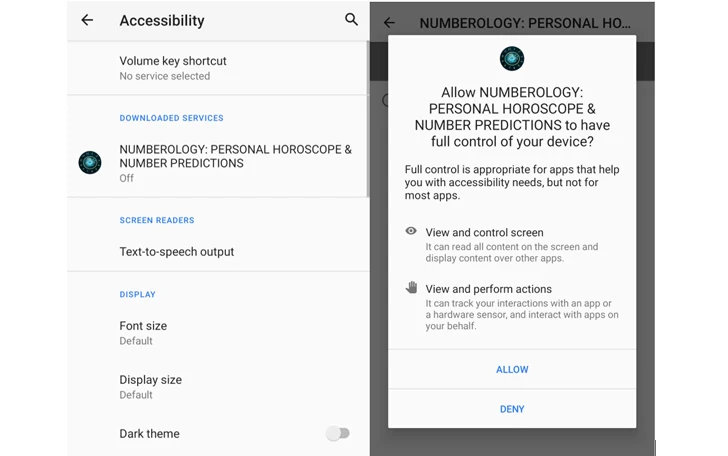
Known vectors: Essential Horoscope for Android (com.anomenforyou.essentialhoroscope) 3D Skin Editor for PE Minecraft (com.littleray.skineditorforpeminecraft) Logo Maker Pro (com.vyblystudio.dotslinkpuzzles) Auto Click Repeater (com.autoclickrepeater.free) Count Easy Calorie Calculator (com.lakhinstudio.counteasycaloriecalculator) Sound Volume Extender (com.muranogames.easyworkoutsathome) LetterLink (com.regaliusgames.llinkgame) NUMEROLOGY: PERSONAL HOROSCOPE &NUMBER PREDICTIONS (com.Ushak.NPHOROSCOPENUMBER) Step Keeper: Easy Pedometer (com.browgames.stepkeepereasymeter) Track Your Sleep (com.shvetsStudio.trackYourSleep) Sound Volume Booster (com.devapps.soundvolumebooster) Astrological Navigator: Daily Horoscope & Tarot (com.Osinko.HoroscopeTaro) Universal Calculator (com.Potap64.universalcalculator)
Wow that's a huge variety of utility apps. And most people are used to granting permissions to apps at this point without considering since most have that pop-up.
Notice that none of them are on F-Droid
Does anyone have any recommendations for protection on phones? I know there is a Malwarebytes app, but is it any good?
I use BitDefender (in the store).
No attempt at attributing the threat actor?