All the cool projects I see while lurking around here have thrown me into the world of Self-Hosting! Some months ago I got myself a NAS, flashed it with TrueNAS and started playing. Today, I am ready to face the creation of my first homelab.
Since I got the basic data storage working, I decided to continue with the Firewall setup. I’d like to have my security figured out before I start spinning up machines, playing with their configs and unwittingly opening all kind of arcane doors to the unknown. So I turn to the Fediverse!
I’d like to create the standard network with a DMZ. Within the network, I plan to use VLANS to manage traffic between devices, and the firewall to limit internet access.
This is a sketch of what I think I want to achieve:
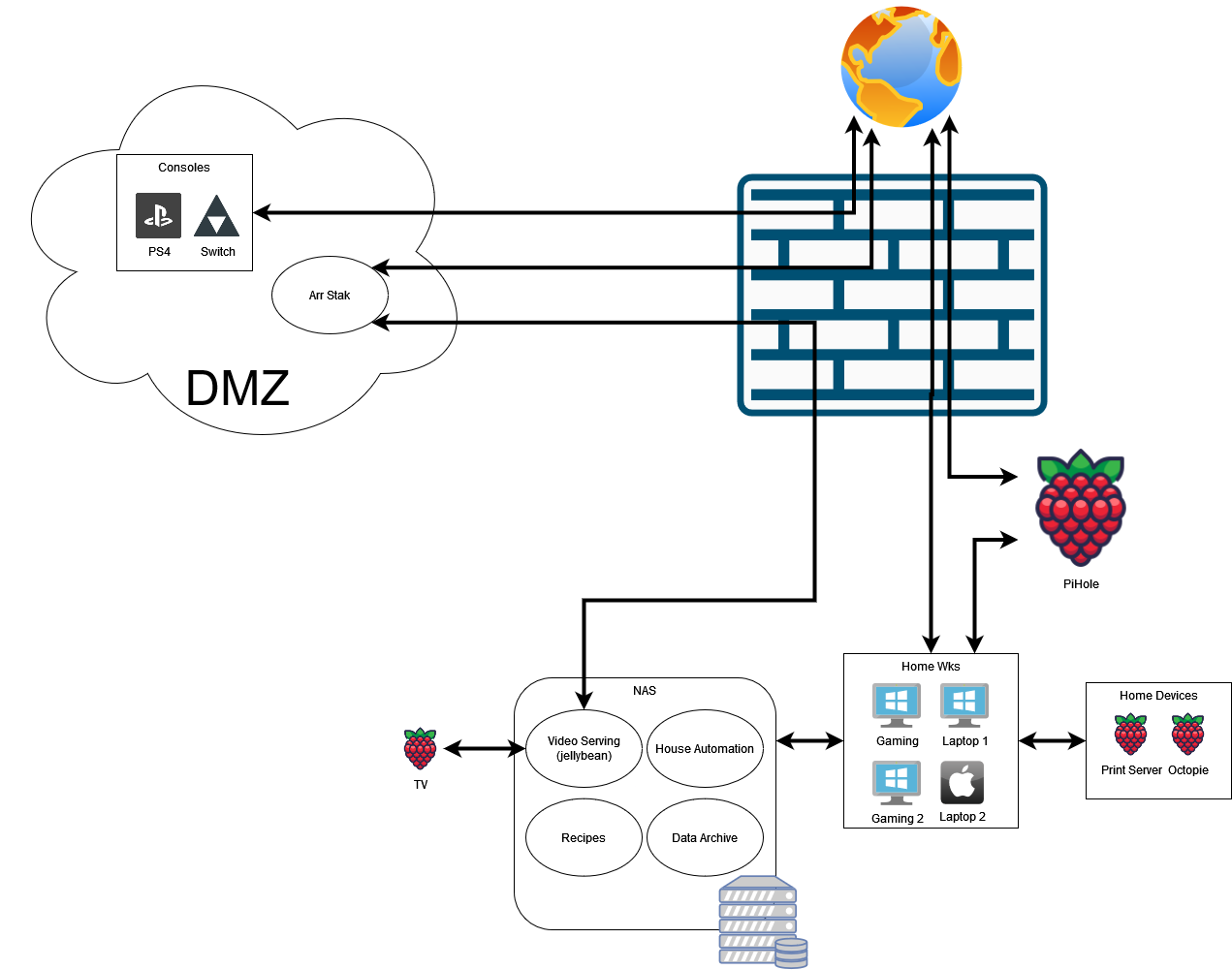
Connections
- The Consoles will connect only to the internet
- The Home Devices (printers) will connect only to the Home WKS
- There will be a NAS device hosting VMs with services accessible only from the home network:
- The Home Automation will connect to IoT
- The Recipes will connect to Home Wks
- The Data Archive will connect to Home Wks
- Jellybean will connect to:
- Home Wks
- TV
- *arr Stack will connect to:
- The Internet
- the NAS (presumably Jellybean)
- The Home WKS connect to pretty much anything
Available Hardware
- OpenWRT compatible Router
- 2.5gbs Unmaged Switch
- 1gbs Unmaged Switch
- QNAS with 2x2.5gbs NIC, running TrueNas
- A few Rpis of different specs
Questions
Firewall
My Main questions relate to the Firewall. It seems that pfsense is the way to go for a SW Firewall:
- What HW should i use? would a Raspberry pi 4, 4GB RAM work?
- What do you think of Netgear 1100?
- I like this device since 3ports would allow me to create a physically separate DMZ
- Should I consider other firewalls?
NAS
For Bonus Points, some questions regarding the NAS:
- With my current diagram, it seems like it is not possible for the NAS to receive updates from the internet. The obvious change is to place the NAS within the DMZ, but I’d like to keep the Data Archive as far from the net as possible
- Should i locate the entire NAS in the DMZ?
- My TrueNas has 2x2.5Gb ports. Can i connect each NIC to a different network? Would this have any benefit?
Thanks for your time!
If you've an OpenWRT compatible router why are you thinking about pfsense? There isn't much to gain there, your OpenWRT will do NAT and also has a firewall.
OpenWRT can do this as well. What are your plans with the DMZ tho?
Be careful with the use of the acronym DMZ as in the context of typical routers and ISPs it has a different meaning of what you're implying here. DMZ usually is used in the context for a single host that is "outside" the ISP router's firewall and all requests coming into the ISP router will be forward to that device.
You NAS will never "receive updates" it will ask for updates. Maybe add a firewall rule that allows traffic from the NAS to the internet but not the other way around (this is usually the default state of any router, it will allow local devices to go to the internet but not incoming connections to those devices).
You can, but is it really worth it? If someone hacks the device they'll access the rest of the network. Same applies to your computers and cames consoles, they can be used to jump to the other side and vice versa.
Frankly I don't see the usefulness of your setup as you'll end up with weak points somewhere. Just get a single OpenWRT router and throw everything into the same network. Apply firewall restrictions as needed.
Great read thank you !
One technical question if you don't mind.
How does that work¿ I mean if the internet traffic isn't allowed to the NAS, how can the NAS get updates than?
Packets initiated from the NAS to the Internet are allowed. Packets initiated from somewhere on the Internet to the NAS are not allowed.
If the NAS requests files from a download server they will be allowed to come through the firewall because the files are a response to a request and not unsolicited traffic. I hope that makes sense.
Ohhh, so if the NAS sends the request, the internet is allowed to send traffic, somehow through a virtual/temporarly port/tunnel.
I didn't knew it worked like that. Do you know what specific subject I need to investigate to learn more about how it works under the hood?
Thanks 👍🖐️
Quick comment to give you a place to start searching; This is called a stateful firewall. Any modern firewall is stateful and tracks connections in a table. When it receives external traffic (packets) associated with a known established TCP connection, it allows that traffic through.
This is also true for UDP and ICMP connections, in case anyone reading wasn't sure. This is how you're able to ping stream and browse from behind your regular firewalls
Thanks 👍
Just note that by default ANY router is configured this way because they run NAT. Traffic originating from the local devices is forwarded to the internet while traffic originating from the internet isn't forwarded to local devices (unless it's a direct rely to a request initiated from a local machine).
I believe this is a good introductory article: https://devopscube.com/what-is-nat-how-does-nat-work/
Thank you !
I do not know if this is different, but I do have some NAT configurations in my Wireguard setup, that forwards all traffic to a protonVPN free tier. I didn't came up with the rules by myself (found some good tutorial on the web)
Is this somehow related on how a router configuration looks like underneath? Or is that totally different?
Thank your for the link :)!!!
More or less... have a look at this: https://www.karlrupp.net/en/computer/nat_tutorial and a tldr at https://serverfault.com/a/564871/122863
Thanks !!
Except for ipv6 (usually). Although most routers will block incoming traffic anyway by default.
Yes, no NAT but the same end result.