this post was submitted on 06 Oct 2024
735 points (90.8% liked)
Technology
59287 readers
5184 users here now
This is a most excellent place for technology news and articles.
Our Rules
- Follow the lemmy.world rules.
- Only tech related content.
- Be excellent to each another!
- Mod approved content bots can post up to 10 articles per day.
- Threads asking for personal tech support may be deleted.
- Politics threads may be removed.
- No memes allowed as posts, OK to post as comments.
- Only approved bots from the list below, to ask if your bot can be added please contact us.
- Check for duplicates before posting, duplicates may be removed
Approved Bots
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
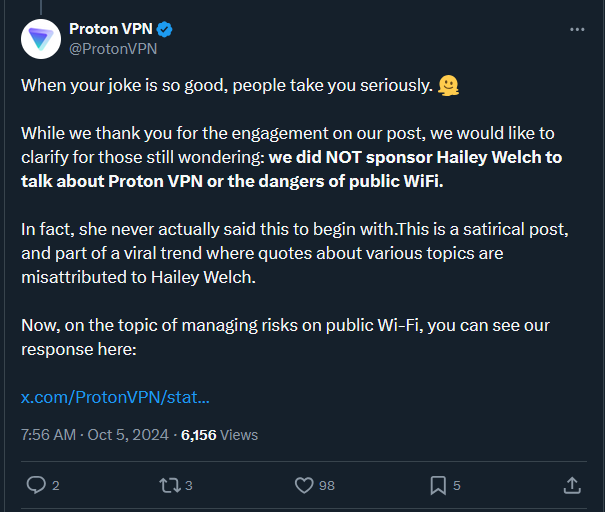
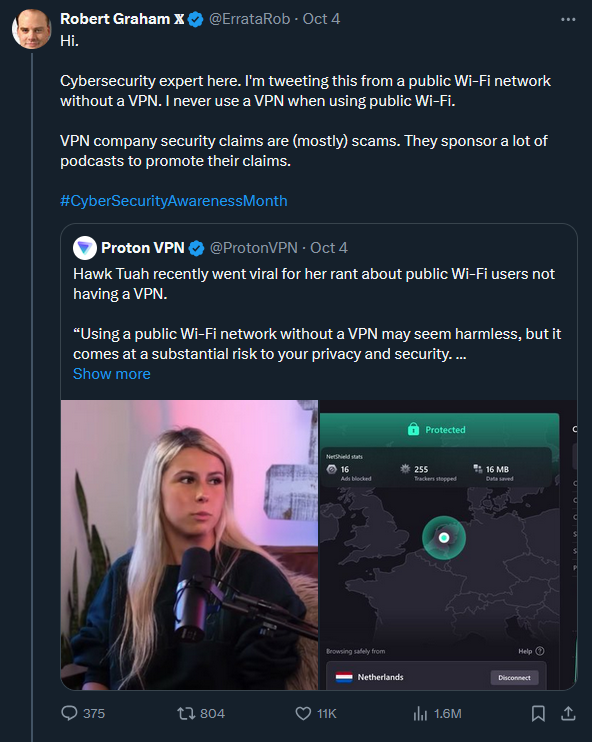
What is he talking about, public WiFi can easily poison and monitor your DNS requests (most people don't know or use encrypted DNS), and there's still tons of non-https traffic leaks all over the place that are plain text. Even if encrypted, there's still deep packet inspection. VPNs can mitigate DPI techniques and shift the trust from an easily snoopable public WiFi to the VPN's more trustworthy exit servers.
This guy really needs to elaborate on what he's trying to say when the cyber security field very much disagrees with this stance. I'm not a huge fan of Proton, but they aren't doing anything wrong here. You should use it for public Wi-Fi.
Yup. You can grab any unencrypted data passed between the user's browser and a server literally out of thin air when they're connected to an open access point. You sit happily at the Starbucks with your laptop, sniffing them WiFi packets and grabbing things off of them.
Oh and you have no idea what the myriad of apps you're using are connecting to and whether that endpoint is encrypted. Do not underestimate the ability of firms to produce software at the absolute lowest cost with corners and walls missing.
If I was someone who was to make money off of scamming people, one thing I'd have tried to do is to rig portable sniffers at public locations with large foot traffic and open WiFi like train stations, airports, etc. Throw em around then filter for interesting stuff. Oh here's some personal info. Oh there's a session token for some app. Let me see what else I can get from that app for that person.
Just FYI https://shop.hak5.org/products/wifi-pineapple. There are ready-made devices that can do basically what you are describing!
Oh nice. Just gotta dress em up like Unifi or Aruba then stick em up on the ceiling.
Yep, my partner gave one for my birthday, it's basically plug-and-play. It can automatically harvest credentials, spoof captive portals, etc. I bet that in most places nobody would question something like this hanging on the ceiling indeed.