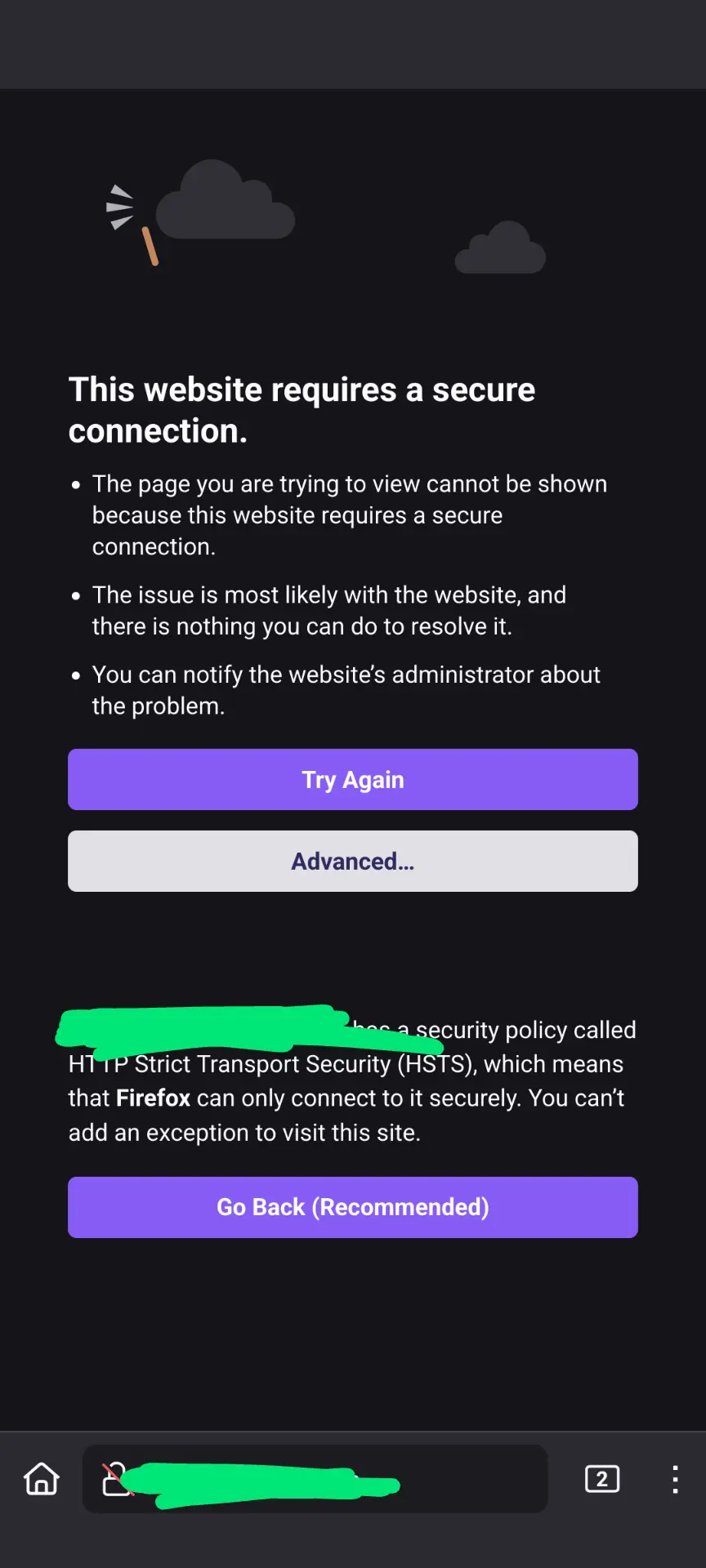
They may block IP addresses associated with consumer ISPs. Assuming that's the case, I would guess you're seeing that as an HSTS/TLS error because their network is trying to trick your browser into redirecting to/displaying an error page hosted by some part of their network.
Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
Once a browser has seen an HSTS flag it will never attempt a non-TLS connection to that site (unless it successfully makes a TLS connection and the flag is gone).
This error is caused by a bad certificate. It can show up if your certificate expired, for instance. It's confusing that the HSTS error takes precedence, I think the bad certificate should take precedence but there you have it.
My money is on the hospital trying to use TLS stripping.
Thanks. I'm past the captive portal and can browse the rest of the internet no problem.
Assuming you're the one adding HSTS, you'll have to inspect the cert and/or view the content that is getting returned. On desktop Chromium you can type "thisisunsafe" to load a page even with HSTS. Not sure how to do it on mobile FF.
Would seem weird for it to be intercepting your domain's traffic but not the rest of the internet.
Edit: just noticed you're not even loading an SSL page. Are you using https in the URL?
https is in the URL, yes. I agree it's weird, especially since my Lemmy instance works. It's hosted by Hetzner but all of the certificate stuff is set up the same way. It could be some sort of residential IP address filter?
Use a Chromium browser to inspect the cert.
If anyone knows how to get Firefox to show a bad cert before loading the page, I'd love to know.
That's... Perversly ingenious
I don't get it. What's it supposed to be doing?
Wifi networks may add popup pages by man in the middeling connections to unsecured sites. However, it's very uncommon to see an unsecured site and people therefore won't see the popup which grants them access after agreeing to the terms of use of the network.
Ohhhhh I see. The wording on that page could be so much better!
I've only had that happen once on public wifi, and just assumed they were doing SSL stripping like you linked. I worked around it by connecting to my Wireguard VPN and routing my traffic through that.
Also, if you know of any good networking Lemmy communities, feel free to share them.
Thanks. Yup, wireguard makes it work. I forgot about that from the last time.
It's still a little curious, though. The certs for my self hosted stuff are done the same was as for the Lemmy instance I'm posting from which I can browse with no problem. The only difference is Lemmy is hosted on Hetzner. Both are behind Nginx Proxy Manager.
You're getting a bad TLS certificate. If you press the Advanced button you should be able to see a reason why the certificate is not accepted by the browser.
It can be any reason, for example I got this error when one of my certificates expired (because I messed around with the DNS API token's permissions and didn't test it afterwards).
In your case it's probably not an expired certificate because then you'd see that error everywhere not just on the hospital WiFi.
I suspect that whoever controls that WiFi is trying to hijack your connection, but it won't work because once a browser has seen a HSTS flag it will refuse to connect to that site in any way except TLS (with the correct certificate ofc).
Kudos for enabling HSTS btw, excellent move.
I'll be very curious to see what the browser says the reason is.
And yes the HSTS error is completely unhelpful in this scenario. The fact HSTS blocks the connection is secondary, the much more important detail is why TLS could not be established.
It's like if your house key didn't work and you were told "you know, doors require a key to be unlocked". You'd be like "dude, I know, I have the key right here, why isn't it working?"
I don't plan on being back at the hospital for a while, so I guess we'll never find out!
I use a wildcard certificate, I wonder how common that is? That might be something they block, but yeah... I wonder why.
FWIW when you can't connect to a website Firefox shows you the "hm we're having trouble finding that site" error.
Nah, wildcard cert wouldn’t play into it at all.
The network is blocking your domain but your browser won't show the block page because the certificate is incorrect.
I've had my domain blocked by a few corporate networks for being "potential spam" or some such nonsense.
A redirect would work. This is not a redirect, it's TLS hijacking. Someone's injecting a bad certificate into OP's connections.
It's probably blocked for whatever reason (maybe less than 90 days old?)
My work and Uni do the same thing, they don't do full SSL inspection, so most websites don't need a custom certificate authority; but if the SNI is blocked then they need a custom certificate to hijack and display a blocked message, most browsers will detect this as a MITM and display a not secure message instead.
Acronyms, initialisms, abbreviations, contractions, and other phrases which expand to something larger, that I've seen in this thread:
| Fewer Letters | More Letters |
|---|---|
| IP | Internet Protocol |
| SSL | Secure Sockets Layer, for transparent encryption |
| TLS | Transport Layer Security, supersedes SSL |
| VPN | Virtual Private Network |
4 acronyms in this thread; the most compressed thread commented on today has 15 acronyms.
[Thread #897 for this sub, first seen 30th Jul 2024, 15:55] [FAQ] [Full list] [Contact] [Source code]